By 2025, global cybercrime will cost a staggering $10.5 trillion annually - yes, trillion with a T! From AI-powered phishing scams that have skyrocketed by 4151% to ransomware attacks costing businesses $53 000 per hour in downtime, the threats we face are becoming more sophisticated, relentless, and expensive.
Whether you're a business owner, security professional, or just someone who wants to keep their personal data safe, these 100 must-know cybersecurity statistics for 2025 will give you a shocking, data-backed look at where we stand - and what’s coming next. Let's check out this year's cyber forecast.
1. Cybercrime and General Cybersecurity Statistics
1.Cybercrime-related damages are expected to reach $10.5 trillion annually by 2025 and could escalate to $15.63 trillion by 2029.
2. Supply chain attacks continue to rise, with 45% of global organizations projected to be impacted by 2025.
3. Business owners worry about the future cybersecurity risks emerging from remote and hybrid work with 72% saying they are concerned.
4. Over 30,000 new security vulnerabilities were identified in 2024, reflecting a 17% year-over-year increase.
5. Attacks on critical infrastructure, financial systems, and communication networks will remain a top cybersecurity threat in 2025.
6. Cybercrime loss projections state they will exceed $23 trillion by 2027, a significant increase from $8.4 trillion in 2022.
7. Social engineering is a part of 98% of cyberattacks – making it a key trend to look out for in the following year.
8. 97% of organizations indicate GenAI issues and breaches are present.
9. The average time required to identify and contain a data breach stands at 258 days, with breaches involving lost or stolen credentials taking 292 days.
10. 24% of organizations think that using GenAI technology will make their incident response more efficient in the future.
11. 53% of companies are actively investing in training staff on how to decrease internal risks.
12. Cyber insurance premiums are forecasted to rise from $14 billion in 2023 to $29 billion by 2027, as businesses seek better financial protection.
13. More than 86% of companies are adopting zero-trust security models in an effort to strengthen their cybersecurity posture.
14. By the end of 2025, up to 60% of organizations on supply chains will start considering the risk of cybersecurity when partnering up with third parties.
15. The FBI’s Internet Crime Complaint Center (IC3) recorded 880,418 cybercrime complaints in 2023, marking a 10% increase from 2022 and estimated financial losses surpassing $12.5 billion.
2. Cybersecurity Threats and Attack Trends
16. Ransomware attacks affected 59% of organizations in 2024, impacting businesses of all sizes.
17. Phishing incidents surged by 4,151% following the public release of ChatGPT in late 2022, as attackers leveraged GenAI.
18. DDoS attacks increased by 13%, totaling 8 million attacks in the first half of 2024.
19. Cryptojacking incidents skyrocketed by 659% in 2023, reaching 1.06 billion recorded attacks.
20. IoT malware grew by 107% in 2024, highlighting an increasing focus on internet-connected devices.
21. Mobile malware attacks are rising, with 6.7 million threats blocked in Q3 2024 alone.
22. Business Email Compromise (BEC) scams are responsible for 25% of all cyber incidents, affecting 70% of businesses globally.
23. 68% of cyber breaches involve human error, emphasizing the effectiveness of social engineering techniques.
24. Social media accounts for 30.5% of all phishing attacks, with platforms like Facebook and Instagram among the most targeted.
25. One of the largest DDoS attacks in 2024 peaked at 3.8 TBps, setting a new record for attack scale.
3. Financial Impact of Cybercrime
26. The global average cost of a data breach reached $4.88 million in 2024, with healthcare experiencing the highest breach costs at $9.77 million.
27. Ransomware-related damages projections hit $265 billion annually by 2031, a dramatic increase from $20 billion in 2021.
28. The average cost of a ransomware attack (per incident) is $1,85 million.
29. The cost of ransom demanded by the attackers averages $2 million, a 500% year-over-year growth.
30. SMBs face an average cost of $120,000 per cyberattack, often struggling to recover.
31. Businesses experience financial losses of $53,000 per hour due to ransomware downtime, while DDoS-related downtime costs $6,130 per minute.
32. The cost of cybercrime is projected to reach almost $14 trillion by 2028.
33. 43% of organizations report losing customers after cyberattacks, showcasing the reputational impact of security breaches.
34. 48% of SMBs have suffered cyberattacks, but 43% are unsure of the security measures they need to take.
35. BEC (Business Email Compromise) attacks cost the companies $4,67 on average, while accounting for 8,5% of all data breaches.
36. The cost of a data breach is the highest in the US, followed by the Middle East, Benelux, and Germany.
37. The U.S. government allocated $12.72 billion for cybersecurity efforts in 2024, excluding the Department of Defense.
38. The cost of recovering from a data breach for small companies is around $120 000.
39. Over a decade, business email compromise attacks have cost businesses more than $55 billion.
4. Cybersecurity Statistics: Workforce and Skills Shortage
40. The global cybersecurity workforce currently includes 5.5 million professionals, yet an additional 5 million experts are missing to fill the skill gap.
41. 46% of organizations report unfilled cybersecurity positions at mid-to-senior levels, reflecting widespread talent shortages.
42. 44% of cybersecurity professionals have less than three years of experience, often due to high turnover and competitive recruitment.
43. The demand for cybersecurity experts is highest in Asia-Pacific, the Middle East, Africa, and North America.
44. 63% of organizations plan on implementing emerging technologies, such as AI, to support the cybersecurity professionals shortage.
45. Projections state that up to 17 300 IT security analyst jobs will open each year over the next decade.
46. Employment demand growth for IT security analysts is higher than the average demand for all other jobs heading into 2023 (29% in particular).
47. 41% of organizations have already leveraged AI to support the decline of the cybersecurity skills gap.
48. Some 40% of C-level executives plan on using AI to support the shortage of critical skills.
49. Predictions state that AI will erase the need for specialized education up to 50% for all entry-level cybersecurity roles by 2028.
5. Industry-Specific Cybersecurity Statistics
Healthcare
50. Healthcare data breaches have been increasing for 14 consecutive years, with 133 million records compromised in 2023.
51. The cost of healthcare breaches declined slightly to $9.77 million in 2024, a 10.6% year-over-year decrease.
52. 68% of healthcare officials say that they witness approximately 2 attacks yearly.
53. By 2025, 90% of healthcare organizations are expected to shift to cloud-based security solutions.
54. Healthcare is the third most targeted industry worldwide.
55. Ransomware attacks targeting the healthcare industry have grown by 25%.
56. Data breach costs for the healthcare sector have dropped by 10,6%.
Manufacturing
57. Cyberattacks targeting the manufacturing sector increased by 41% in the first half of 2024.
58. Ransomware accounted for 29% of global attacks on manufacturers in Q2 2024, a 56% increase from the previous year.
59. Estimates show that 44% of computers in the retail industry are affected by ransomware.
60. In the manufacturing industry, 62% of victims pay the demanded ransom to the attacker.
61. The average cost of a data breach in the manufacturing industry has grown 18% year-over-year.
62. The manufacturing industry accounts for 6% of all worldwide data breaches yearly.
63. The cost of a data breach in the manufacturing industry averages $3,48 million.
Finance & Insurance
64. The finance sector remains a primary target for cybercriminals, particularly for BEC and ransomware attacks.
65. 78% of financial institutions reported experiencing ransomware attacks in 2024, with the average breach costing $5.9 million.
66. Financial institutions are top targets for deepfake AI attacks.
67. Financial services companies are experiencing a 65% year-over-year growth when it comes to API and web application attacks.
68. Based on phishing alone, financial services organizations are the third most attacked industry.
69. The cost of a data breach in the financial industry increased 2,3% year-over-year.
70. The average cost of a single data breach in the finance industry is $5,9 million.
Education
71. The education sector faced more cyberattacks than any other industry in Q2 2024.
72. Ransomware incidents in education cost an average of $3.65 million per breach.
73. The goal of 95% of ransomware attackers is to gain access to data backups.
74. The cost of downtime (daily) for the education industry can reach up to $550 000.
75. Over a five-year period, ransomware caused data breaches to cost the education sector around $53 billion in downtime.
6. AI and Cybersecurity Statistics
76. 85% of cybersecurity professionals believe AI is making cyberattacks more frequent and sophisticated.
78. GenAI breaches and security issues are reported by 97% of organizations.
79. AI-driven attacks are expected to account for 17% of all cyber threats by 2027.
80. 70% of organizations say AI significantly enhances threat detection and response.
81. GenAI-supported phishing attacks trick 60% of recipients, significantly higher compared to traditional phishing.
82. Estimates say that 80% of phishing scams are AI-supported, forecasting the trend will likely continue.
83. Free GenAI tools, such as ChatGPT, can produce around 30 phishing email templates hourly.
84. The use of AI aids organizations to find data breaches 107 days earlier than companies who don't leverage AI.
85. Cybersecurity costs can be reduced by $2,2 million yearly if the company decides to invest in Automation Tools and AI.
86. The AI cybersecurity market projections state it will reach $133 billion by 2030.
87. Organizations that actively use AI and security automation can save up to $1,8 million yearly on data breaches, compared to organizations that don't.
88. 53% of companies admit they do not feel prepared for cybersecurity risks posed by AI.
89. 41% of organizations are already using AI to counter cyber alert fatigue.
7. Security Investments and Trends
90. Spending on global information security is projected to increase by 15% in 2025.
91. Research suggests yearly cybersecurity spending projections are at $183,9 billion.
92. The average year-over-year growth for cybersecurity budgets is 8%.
93. A form of zero-trust architecture, Identity and Access Management (IAM), is expected to exceed market worth of $24 billion by the end of 2025.
94. Up to 41% of organizations today use some sort of zero-trust security architecture.
95. 83% of Information Technology professionals in SMEs require using MFA.
8. Cyber Insurance Statistics
96. Global cybersecurity insurance premiums will grow from $14 billion to $19 billion in 2027.
97. Claims made on cybersecurity insurance are growing 13% year-over-year.
98. Cyber insurance carriers report average losses of around $100 000 per claim.
99. 74% of organizations have cybercrime insurance to cover for potential losses.
100. Ransomware was responsible for 19% of all claim reports to cyber insurance.
101. The market size of cyber insurance is expected to top $20 billion.
102. Companies invest an average of 12% of Information Technology budgets on cybersecurity measures.
Cybersecurity Statistics 2025 Wrap Up
It's important to recognize that merely knowing cybersecurity statistics isn't sufficient for safeguarding your assets. These figures should serve as a tool to communicate the real and present dangers of cyber threats, helping you to secure buy-in from both executives and team members. By emphasizing how strategic investments in cybersecurity can mitigate risks and protect organizational interests, you can make a compelling case for increased security measures. Highlighting specific statistics from this data can illustrate potential vulnerabilities and the financial implications of breaches, reinforcing the value of proactive security investments.
Sources
Statista, Gartner, SkyboxSecurity, World Economic Forum, IBM, Ponemon Institute, Sophos, SlashNext, SonicWall, Netscout, Kaspersky Lab, Arctic Wolf, Verizon, APWG, Cloudflare, Cybersecurity Ventures, Hiscox Cybersecurity Report, Sage Group, HIPAA Journal, DuploCloud, Ontinue, Check Point Research, Bridewell, Critical Start, Bitdefender, Imperva, CFO, Capgemini, VikingCloud, Securonix, Cisco, Sprinto, KPMG, Securityintelligence, Astra, HoxHunt, Infosecurity Magazine, Coalition, NetworkAssured, PurpleSec, PentestPeople, Security Magazine, Delphiix, Allianz, Forbes, Veeam, Integrity 260, Harvard Business Review, Abnormal Security, Heimdal, IC3, ProofPoint, Thales Group, Cynerio, Cloudflare, CSO, HelpNetSecurity, DarkReading, VeraCode, Secureframe, Akamai, ThreatDown, Varonis, JumpCloud, Cyberseek, ComputerWorld, Google Cloud, Beyond Trust, BreachSense, Clear Insurance.
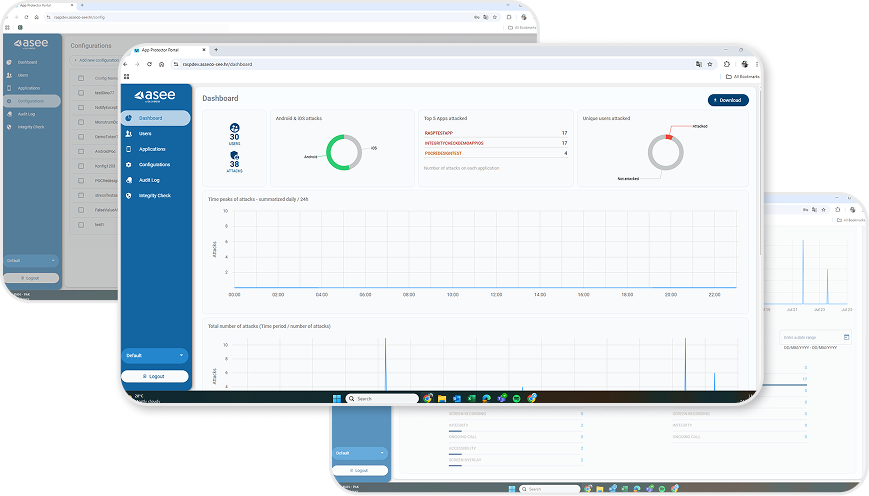
eBook: Beyond the Basics: A C-Suite Checklist for Banking Security Strategy
To guide you toward developing and maintaining a secure banking security strategy, ASEE offers a detailed security checklist to assist you in the process.
Feel free to contact us – zero obligation. Our ASEE team will be happy to hear you out.