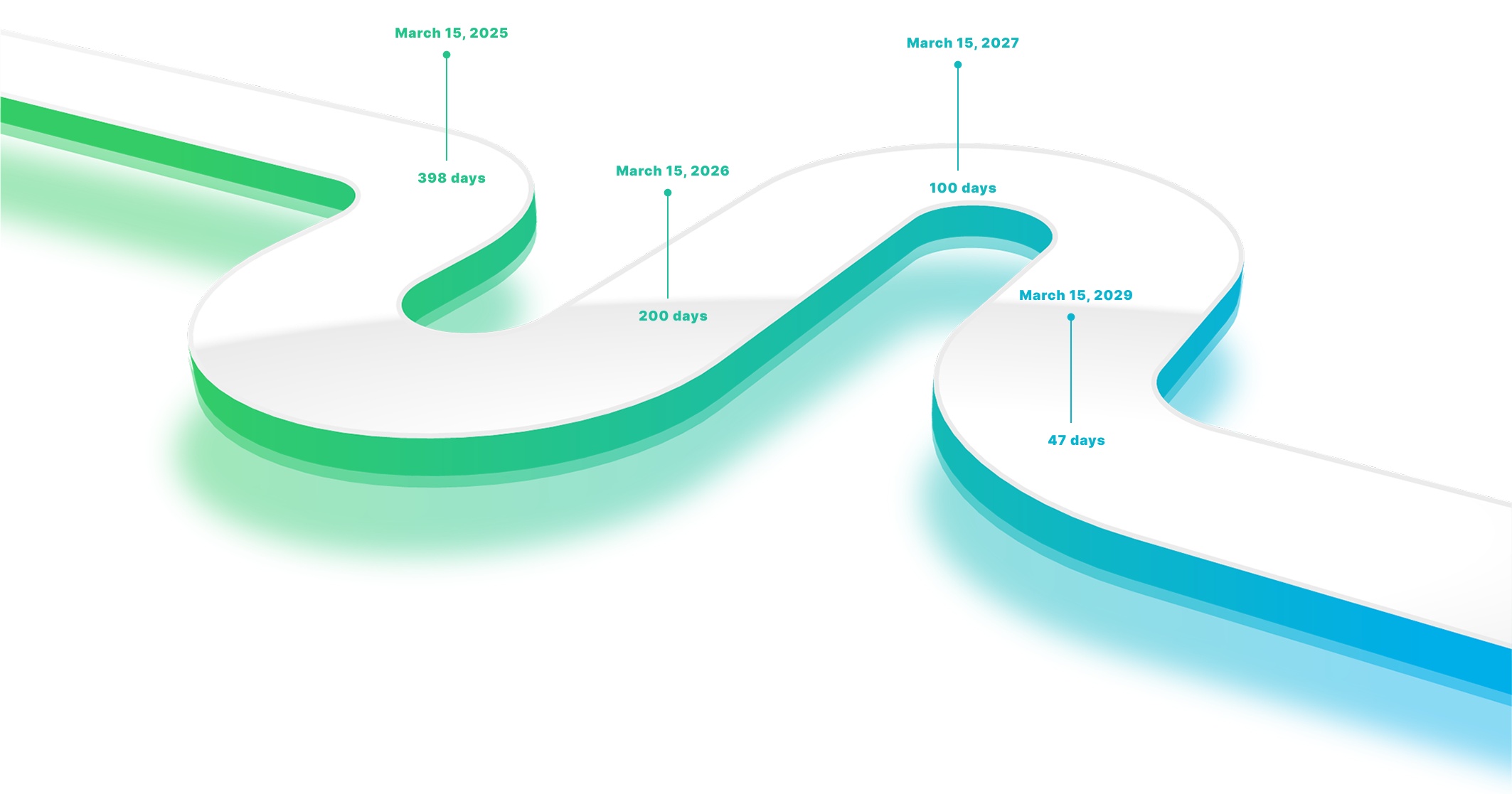
TLS/SSL certificate validity periods are rapidly decreasing, increasing operational pressure on IT teams and significantly raising the risk of missed renewals. From 398 to 47 days by 2029, what used to be multi-year validity periods is now moving towards days. Shorter lifespans, compliance requirements, and the growing number of machine identities make manual TLS/SSL certificate management unsustainable.
Certiligent is an automated TLS/SSL certificate lifecycle management platform that continuously monitors, renews, and replaces TLS/SSL certificates before expiration without manual intervention.
Designed for companies where reliability, security, and availability are critical, Certiligent removes the operational risk associated with manual certificate management.








Interested in more details about how Certiligent works? Download the datasheet.